Three of the largest password managers fail to deliver on their core security promise—even when using end-to-end encryption. A new study from ETH Zurich and Universita della Svizzera Italiana exposes multiple attack vectors that could allow unauthorized access to encrypted vaults, directly contradicting the 'Zero Knowledge' claims made by LastPass, Bitwarden, and Dashlane.
The research team, after dissecting the cryptographic workflows of these services, identified a pattern of vulnerabilities tied to how shared vaults handle key distribution and recovery. In one scenario, an attacker could manipulate the encryption keys exchanged during account recovery or new member invitations, effectively bypassing the vault’s protections.
- Key escrow flaws: Shared vaults generate multiple keys during recovery or new member invitations. If these keys aren’t properly verified, attackers could substitute their own keys during transmission, decrypting the vault’s contents.
- Account takeover risk: In some cases, an attacker could gain full access to a shared vault immediately after a new member accepts an invitation—before the legitimate user even logs in.
- Server-side exploitation: The study also models a worst-case scenario where a fully compromised server could deviate from expected behavior, further eroding security guarantees.
The researchers emphasize that these vulnerabilities aren’t theoretical. In practice, they could allow an insider with server access—or an external attacker who infiltrates a provider’s systems—to recover passwords directly, defeating the purpose of encrypted storage.
How the attacks work
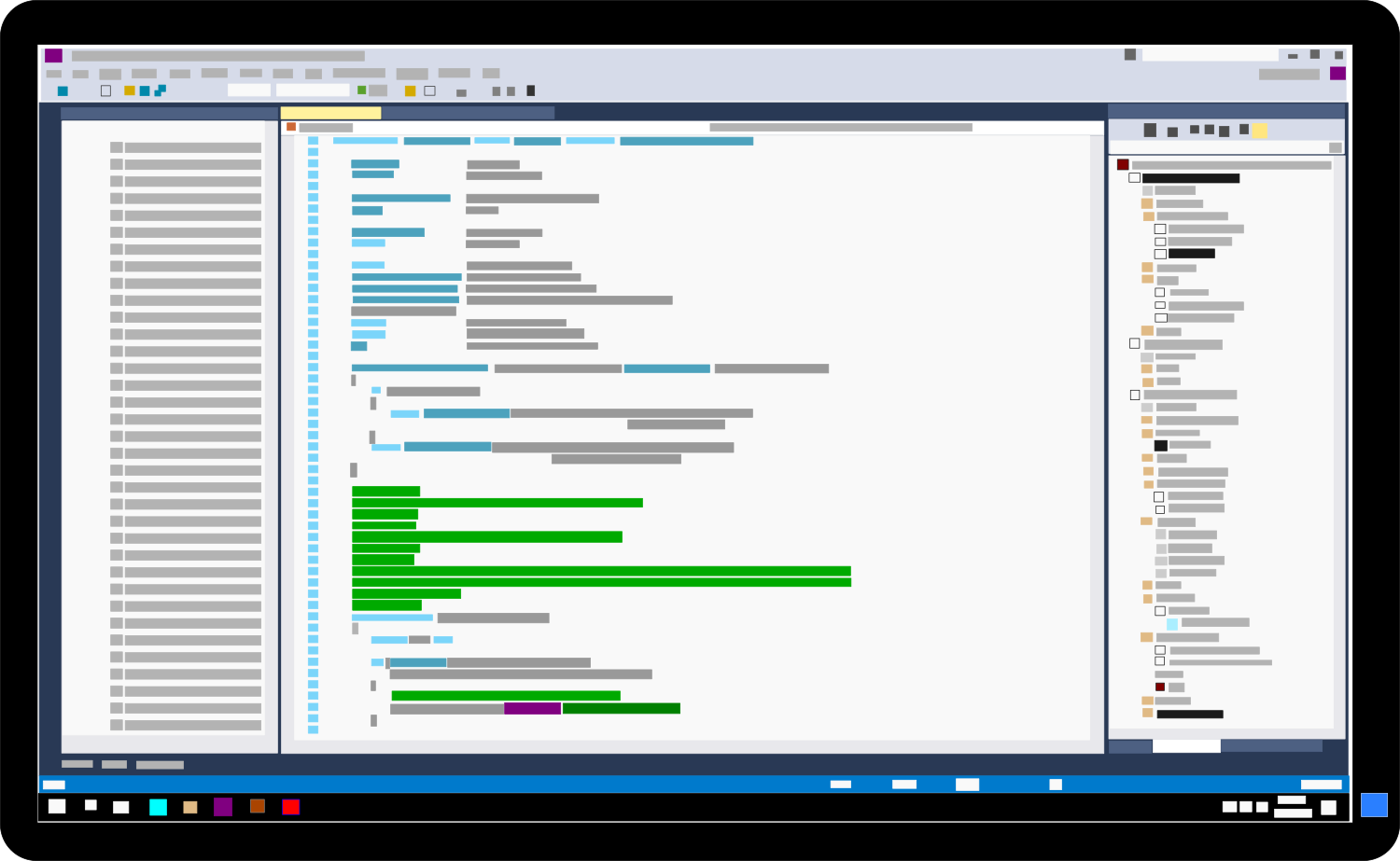
When a shared vault administrator resets a forgotten access code or invites a new user, the service generates a set of cryptographic keys. These keys are sent to the client device, bundled, and re-encrypted before being returned to the server. The flaw lies in the fact that some password managers do not validate whether these keys remain unchanged during transmission. An attacker intercepting the process could swap in a malicious key pair, allowing them to decrypt the vault’s master key upon receipt.
This isn’t just a risk for enterprise or high-profile users. The study highlights that even individual accounts using shared vaults—such as family or team logins—are exposed. Once an attacker gains control of the vault’s key, they could reset passwords for all members, effectively locking out legitimate users while gaining full access.
What does this mean for users?
Despite these findings, password managers remain a critical tool for securing online accounts—especially when compared to weaker alternatives like reused passwords or unencrypted notes. However, users should take additional precautions
- Use a separate, offline recovery password that isn’t stored in the vault itself.
- Enable two-factor authentication (2FA) via a dedicated authenticator app or hardware key, not tied to the password manager.
- Avoid sharing sensitive vaults unless absolutely necessary, and limit administrative privileges.
The study underscores a broader industry challenge: even well-intentioned security measures can unravel when implementation details are overlooked. While providers like LastPass and Bitwarden have not yet commented on the findings, the research serves as a wake-up call for the entire sector to re-examine how 'Zero Knowledge' encryption is applied in real-world scenarios.
For most users, the risk remains low—but the stakes couldn’t be higher if exploited. The takeaway? Assume no system is foolproof, and layer your defenses accordingly.