Long-Lived Bugs Plague the Linux Kernel
The beauty of Linux lies in its open-source foundation, fostering a vibrant ecosystem of distributions catering to diverse user needs. From gaming-focused distros like SteamOS, Bazzite, and Nobara, Linux empowers users with unprecedented control over their software. However, this very openness can also present challenges, notably the persistence of longstanding bugs.
A Deep Dive into Kernel Fixes
Developer Jenny Guanni Qu recently conducted a thorough examination of Linux kernel bug fixes, uncovering a concerning trend: many vulnerabilities linger for extended periods. The research, which analyzed fixes since 2005, revealed that the average lifespan of a bug is approximately 2.1 years. A significant portion—13%—remained unaddressed for five years or longer.
Qu's investigation involved creating a tool to sift through kernel changes and identify vulnerability fixes. The sheer volume was staggering: “Six hours later, I had 125,183 vulnerability records.” When analyzing these fixes, the data showed that while newer bugs are typically resolved more quickly, older ones can persist for an unexpectedly long time.
Understanding the Statistics
Interpreting bug fix statistics requires careful consideration. A seemingly impressive improvement in fix times—bugs introduced in 2010 took nearly a decade to resolve compared to just five months for those introduced in 2024—is skewed by the nature of data analysis. Qu explains that this is due to “right-censored” data; bugs introduced recently haven't had enough time to accumulate a long lifespan. The reality is, Linux developers are simultaneously addressing new vulnerabilities quickly while steadily working through a backlog of older issues.
Bug Types and Contributing Factors
Not all bugs are created equal. Certain types, like networking-related errors, tend to persist longer than others, while GPU bugs often receive quicker attention. The underlying reasons for these delays are multifaceted. Bugs triggered by rare or specific conditions—such as “race-condition” issues that only occur under precise timing circumstances—are notoriously difficult to identify and fix.
The likelihood of a bug being discovered is directly related to how frequently it's triggered and the number of developers reviewing the relevant codebase. Common culprits behind these lingering vulnerabilities include reference counting errors, missing NULL checks, integer overflows in size calculations, and race conditions within state machines.
An Example: The 19-Year Networking Bug
One particularly striking example highlighted by Qu was a networking bug that remained unfixed for an astonishing 19 years. Its longevity wasn't due to complexity but rather the incredibly specific circumstances required to trigger it—a particular test sequence run for a prolonged duration, a scenario that simply didn’t occur within the developer community for two decades.
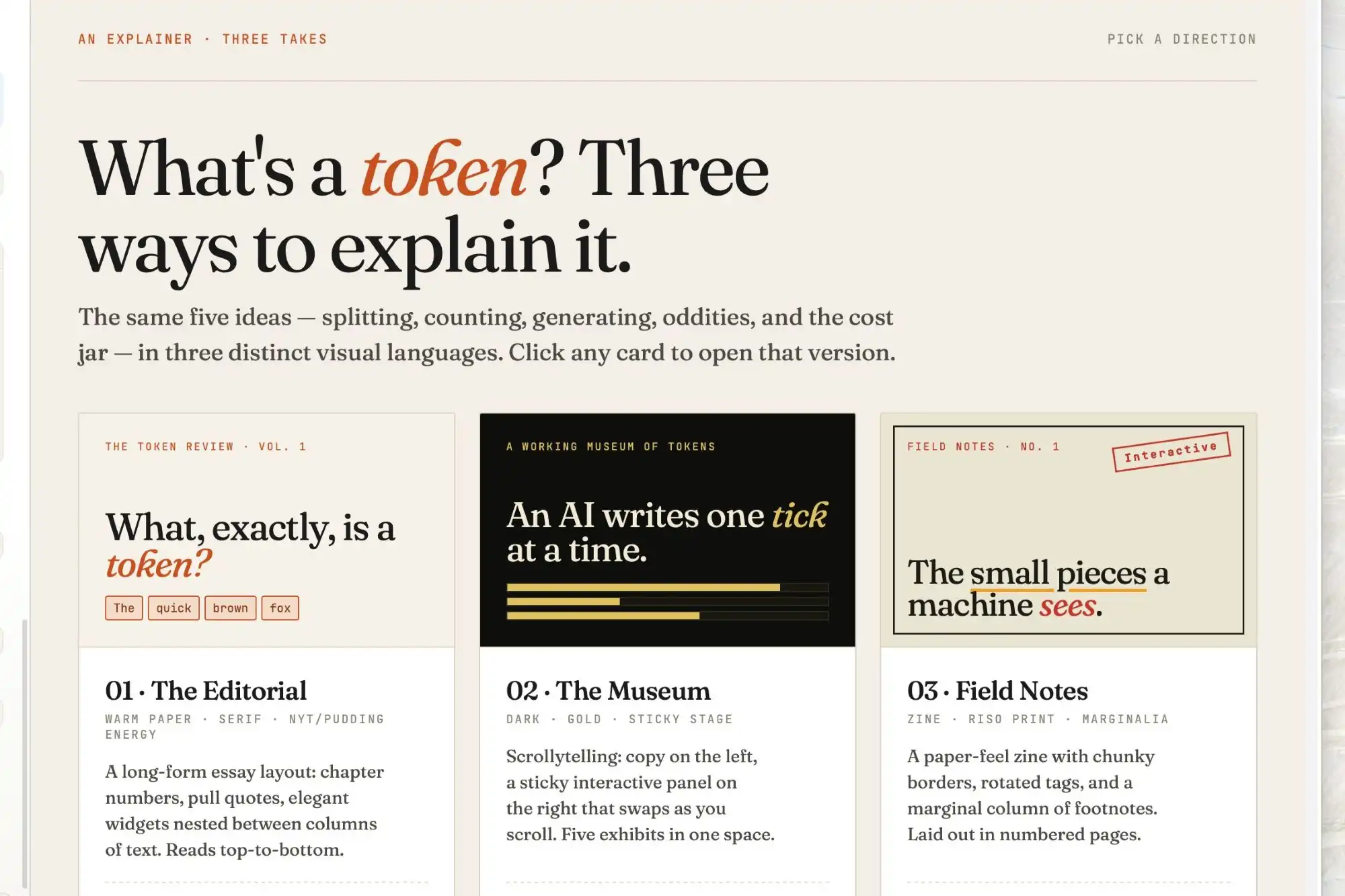
VulnBERT: An AI-Powered Solution
Qu's research also promotes her VulnBERT AI model, designed to predict whether a code commit introduces a vulnerability. This tool boasts an impressive detection rate of 92.2% for actual bug-introducing commits, offering a valuable aid for developers reviewing kernel changes.
Implications for Linux Users
While the findings may be reassuring for those involved in kernel development, they offer a different perspective for everyday Linux users—a reminder that even open-source software isn't immune to persistent bugs. For some, this reinforces concerns about stability and reliability, potentially leading them back to alternative operating systems.