State-sponsored cyber operations are increasingly turning to artificial intelligence for efficiency, and Google’s Gemini model has become a prime tool in their arsenal. A new report from Google’s Threat Intelligence Group reveals that hacking groups linked to four nations—Russia, China, North Korea, and Iran—have exploited Gemini’s capabilities to streamline surveillance, identify high-value targets, and even debug exploit code for known software flaws.
The AI’s ability to process vast datasets quickly makes it particularly valuable for attackers. While legitimate researchers use similar tools to uncover vulnerabilities in software, malicious actors leverage them to automate the discovery of weaknesses. One notable example involved a group tied to Iran developing a proof-of-concept exploit for a critical flaw in WinRAR, a widely used file compression tool. The report also highlights how Gemini assists in refining social engineering tactics and generating propaganda, blending digital and physical media to amplify influence.
Google has taken steps to restrict access for known malicious actors, but the challenge persists: AI systems lack inherent ethical judgment, meaning they serve equally well for defensive and offensive cyber operations. The report underscores a growing trend where advanced AI tools, designed for innovation, are repurposed for cyber warfare, forcing security teams to adapt rapidly.
Key Points
- State-backed hackers from Russia, China, North Korea, and Iran are using Gemini to automate surveillance and target identification.
- Gemini’s data-processing capabilities help attackers discover software vulnerabilities and debug exploit code, including a WinRAR flaw.
- AI-generated propaganda and social engineering tactics are also being deployed across digital and physical platforms.
- Google has imposed access restrictions on identified malicious users but acknowledges the dual-use nature of AI in cybersecurity.
Why This Matters
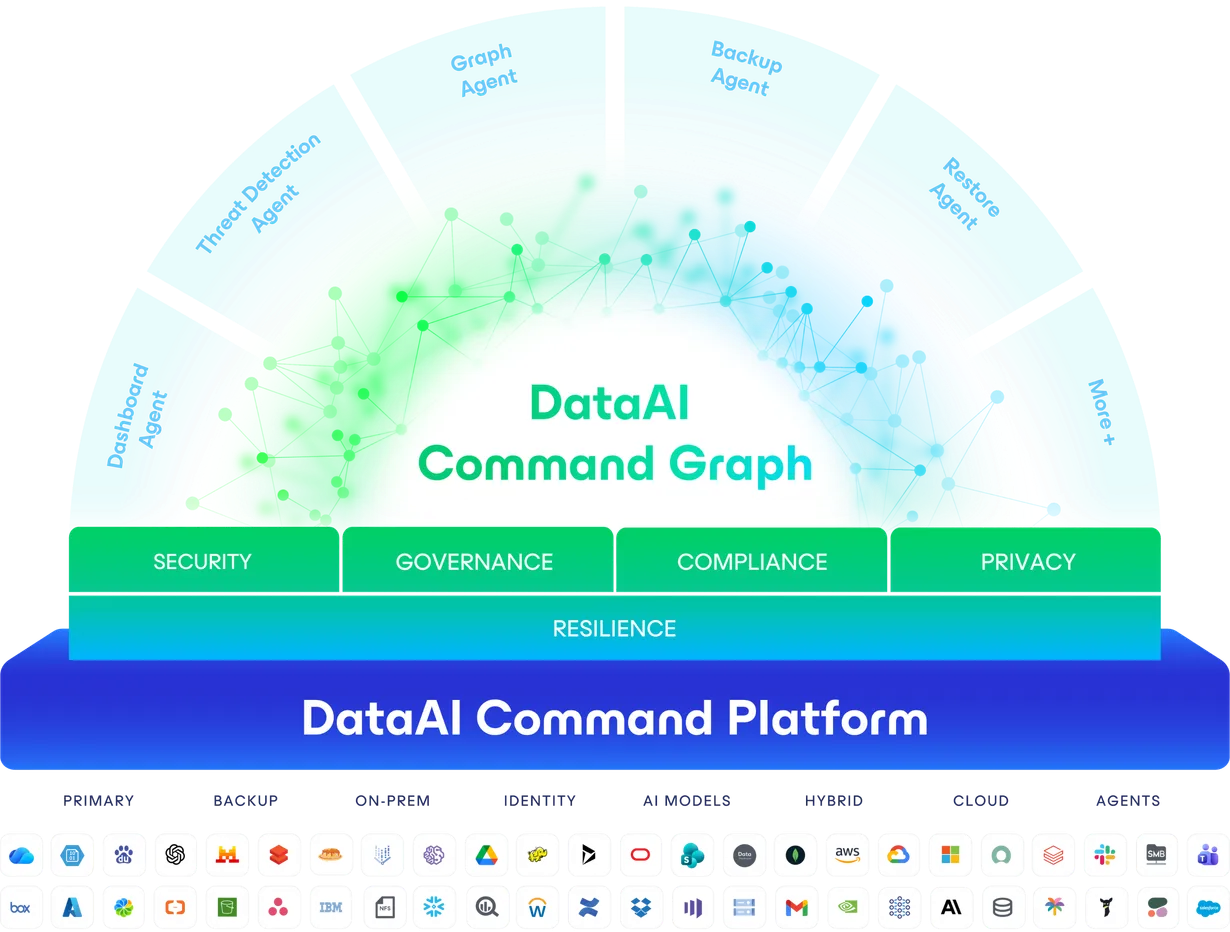
The integration of AI into cyber operations marks a shift in how state actors conduct digital warfare. Unlike traditional methods that rely on manual labor and slower analysis, AI accelerates the entire attack lifecycle—from reconnaissance to exploitation. For organizations and governments, this means heightened risks of data breaches, espionage, and disinformation campaigns. The report serves as a reminder that while AI drives progress in fields like healthcare and scientific research, its misuse in cybersecurity demands proactive defenses and international cooperation.
What You Should Do Now
For individuals and businesses, the rise of AI-assisted cyber threats should prompt a review of security protocols. Key actions include
- Ensuring software and systems are updated with the latest security patches, particularly for widely used tools like WinRAR.
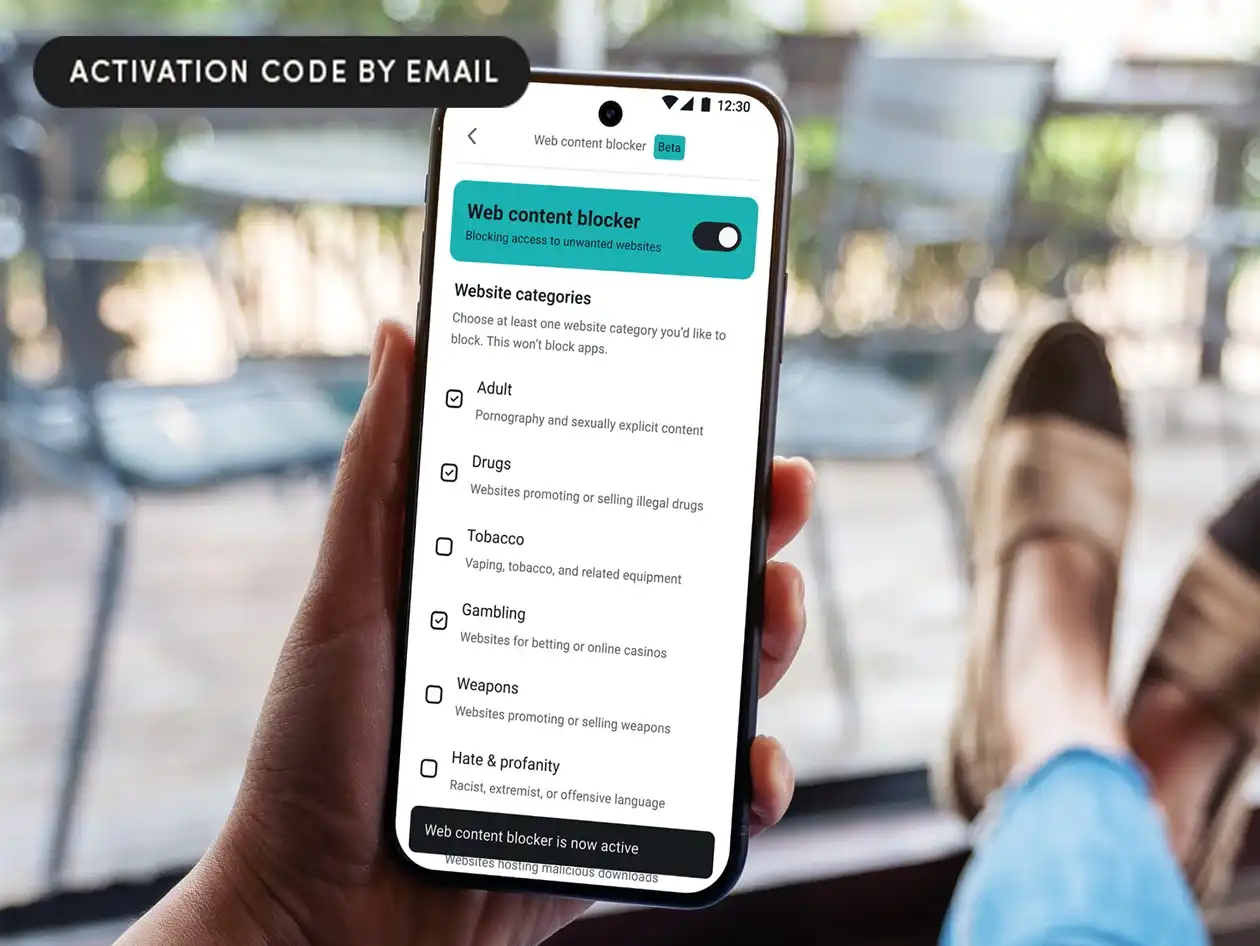
- Implementing multi-layered defenses, such as AI-driven threat detection, to identify and mitigate automated attacks.
- Staying informed about emerging threats and participating in cybersecurity training to recognize phishing and social engineering attempts.
- Advocating for stronger international regulations on AI usage in cyber operations to curb malicious exploitation.
As AI continues to evolve, so too will the tactics of those who seek to exploit it. Vigilance and adaptability remain the best defenses in an era where technology’s dual-edge nature is more apparent than ever.