

The surge in AI-driven workloads is putting unprecedented pressure on RAM supplies, with industry experts warning of long-term supply shortages and cost instability. Micron's analysis reveals a growing mismatch...








A limited-time offer for Microsoft Office allows one-time purchase of the full suite, including Word, Excel, and Po...

The NVIDIA RTX PRO 6000 delivers the performance of four RTX 5090 GPUs in AI training while consuming only a quarte...

The global DRAM market faces prolonged supply shortages, with manufacturers projected to meet only 60% of demand th...

The TP-Link Archer BE230 delivers dual-band Wi-Fi 7 speeds at a price far below typical launch costs, challenging t...

A new MacBook series drops with a focus on thermal design and battery life, but the real story lies in how it force...
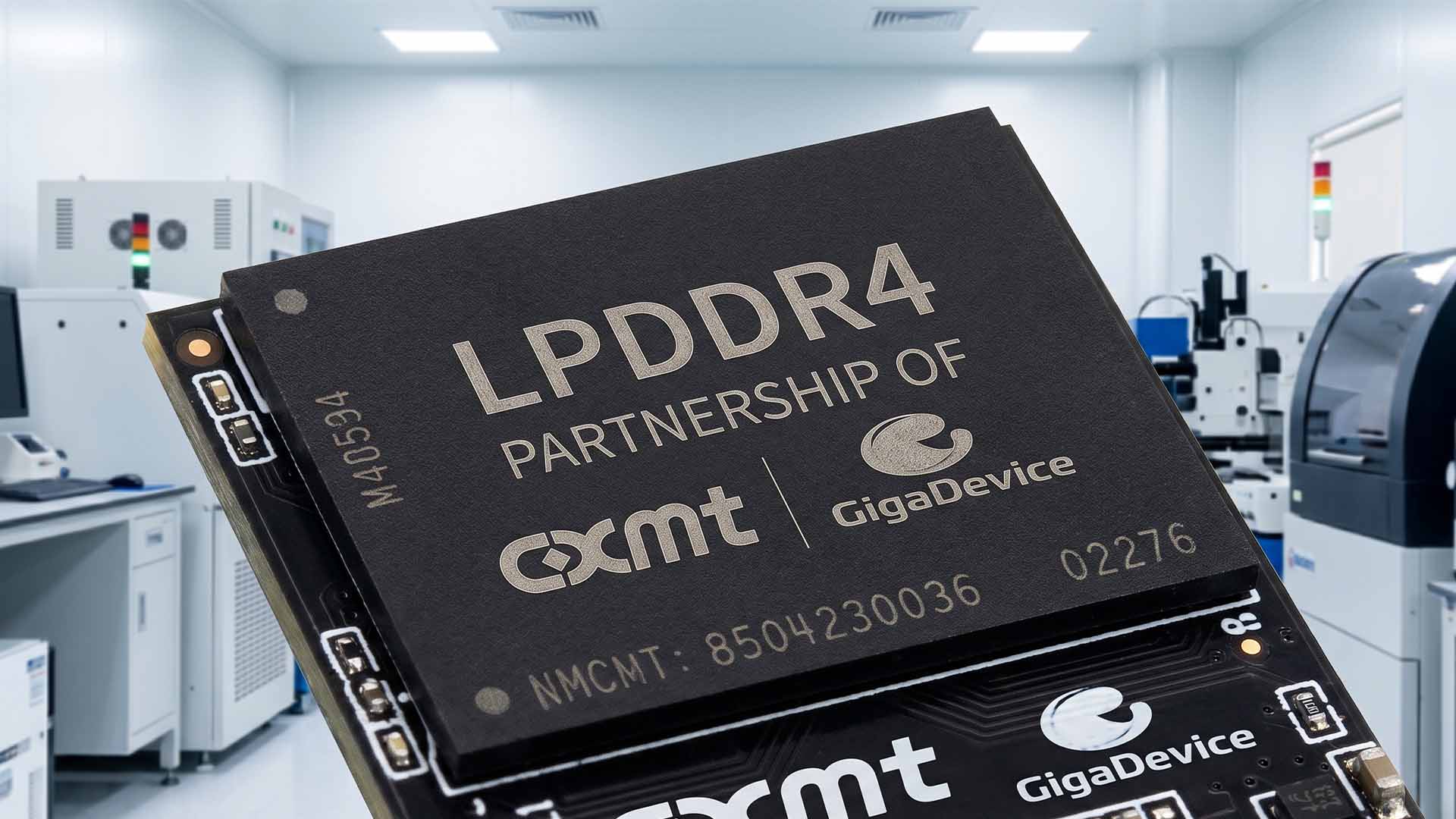
Chinese DRAM manufacturers are rapidly increasing production of LPDDR4 memory, aiming to replace Samsung’s supply a...
Intel's upcoming Nova Lake processors introduce a significant cache advantage, outpacing AMD's Ryzen 9 9950X3D2 in...

A new era of modular cooling has arrived with the Epomaker RT98, offering unmatched thermal performance and flexibi...

A new configuration of the 14-inch M5 MacBook Pro emerges, offering 24GB of unified memory and a 1TB SSD at a reduc...

Memory and SSD prices have skyrocketed, forcing gamers to weigh performance gains against steep costs as manufactur...





