The DDR6 standard is poised to redefine performance benchmarks with speeds up to 17,600 MT/s, but its adoption hinges on overcoming significant engineering challenges. This article explores the tradeoffs behind...




A new behind-the-scenes documentary offers an intimate look at the creation of Masters of Albion, revealing the tea...

The Turris Omnia NG Wired router offers 10 Gbps connectivity, designed for rack mounting with a focus on security a...

A new update to NVIDIA's cloud gaming service introduces high-refresh streaming at 4K resolution, specifically targ...
A glimpse into the future of The Last of Us series reveals new details about development and release timing, offeri...

Prime Video's Fallout Season 2 has achieved record viewership with 83 million viewers, setting a new benchmark for...

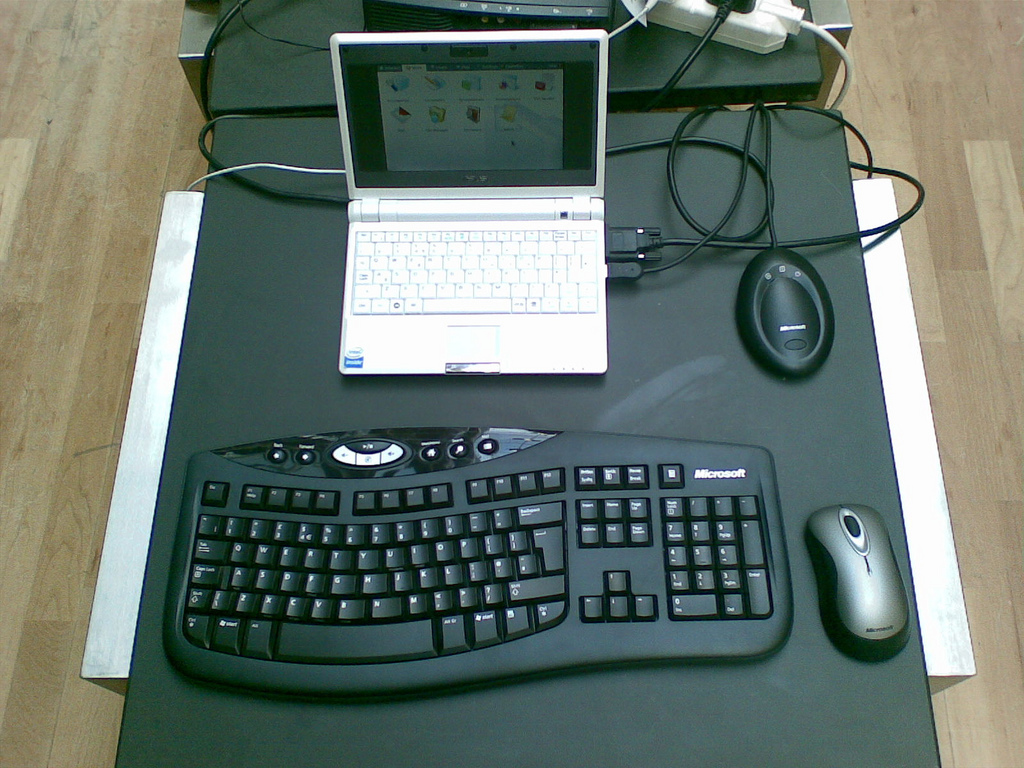
A one-time, permanent Microsoft Office license now costs less than a Starbucks coffee—if you can handle the fine pr...

The new Acer FA300 brings PCIe 5.0 speeds to a wider audience with 1 TB and 2 TB capacities, offering up to 11 GB/s...
A new generation of digital twin platforms is reshaping urban planning by integrating real-time data analytics with...

The virtual hangout space Rec Room, which once boasted over 150 million registered players, has announced an immedi...

NVIDIA has unveiled new performance benchmarks for the RTX 50 series, offering a closer look at what these GPUs can...