A newly discovered Linux vulnerability allows attackers to bypass security checks and gain elevated system access, posing a serious risk to servers and workstations. Experts warn of active exploitation attempts...


Allegations that Gunzilla Games has left dozens of employees unpaid for months threaten to expose systemic failures...

The Lenovo Yoga 7i OLED introduces a 14-inch 90Hz OLED touchscreen with a 360-degree hinge, combining smooth visual...

The 'Send to' menu in Windows 11 has become a cluttered, inconsistent tool. Developers can streamline it in seconds...

A newly discovered vulnerability in TP-Link routers could expose small businesses to state-sponsored cyberattacks,...

The Kamrui Hyper H2 packs an Intel Core i7-1065G7 and 16 GB of RAM into a 9.8-inch square chassis, delivering deskt...

A recent driver update brings basic compatibility to Intel's Arc GPUs in Crimson Desert, though performance and fea...

GeForce NOW introduces a lineup of demanding new titles, including 'Samson' and 'Morbid: The Second Omen,' targetin...
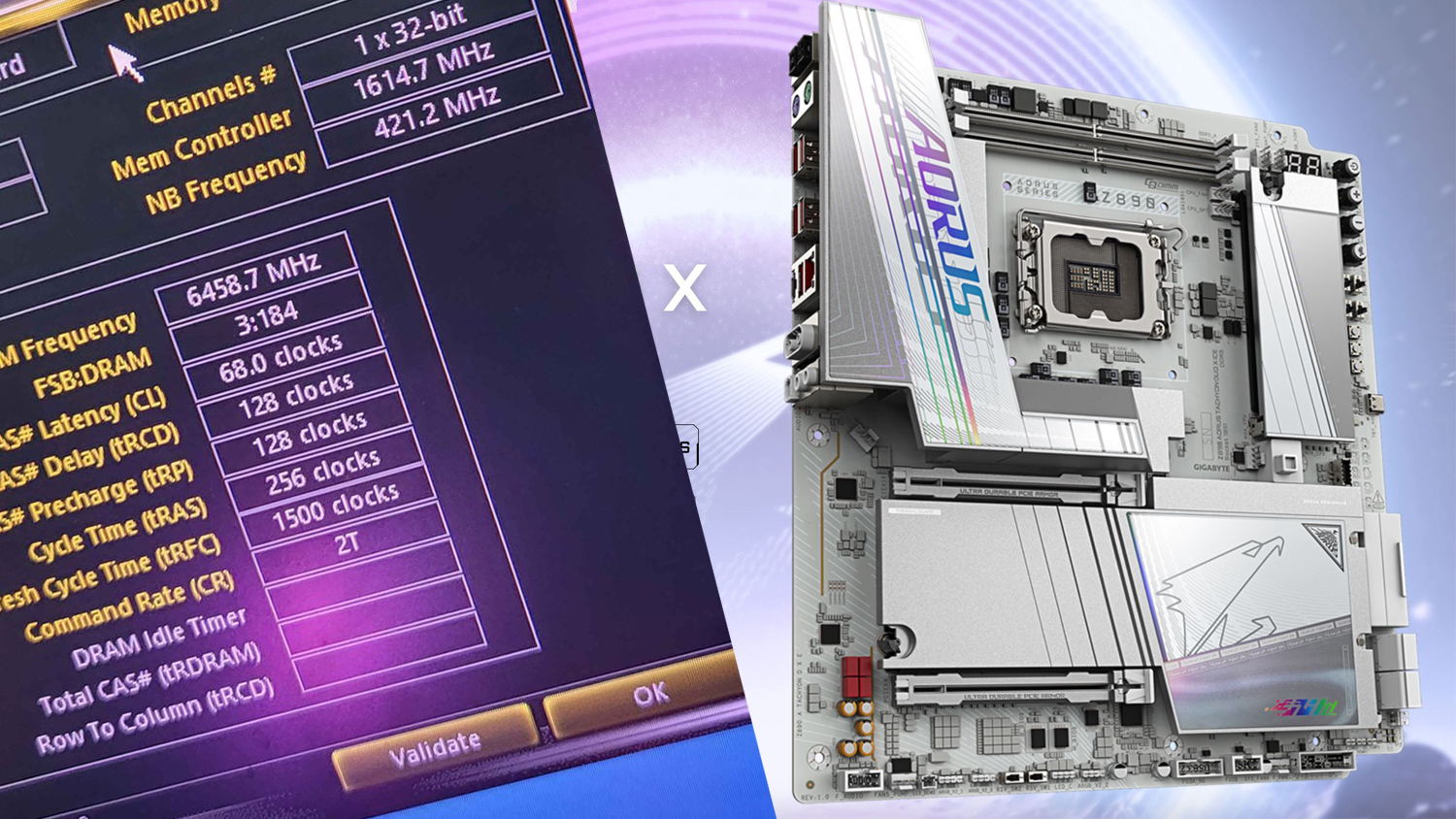
A new overclocking benchmark for DDR5 memory has been set at 12,917 MT/s using a GIGABYTE Z890 AORUS Tachyon DUO X...

The Logitech MX Vertical ergonomic mouse is now available at a significantly reduced price of $75, down from its or...
A new multiyear partnership between Intel and Google will focus on advancing AI systems using Xeon processors and c...