Rockstar Games is adopting a console-first strategy for its next-generation titles, including the highly anticipated GTA 6. This shift reflects broader industry trends where hardware optimization and platform e...





The ninth mainline Resident Evil game has sold over five million copies since its late-February launch, securing a...

Respawn and EA are implementing stricter anti-cheat measures in Apex Legends, targeting devices like Strikepacks, C...
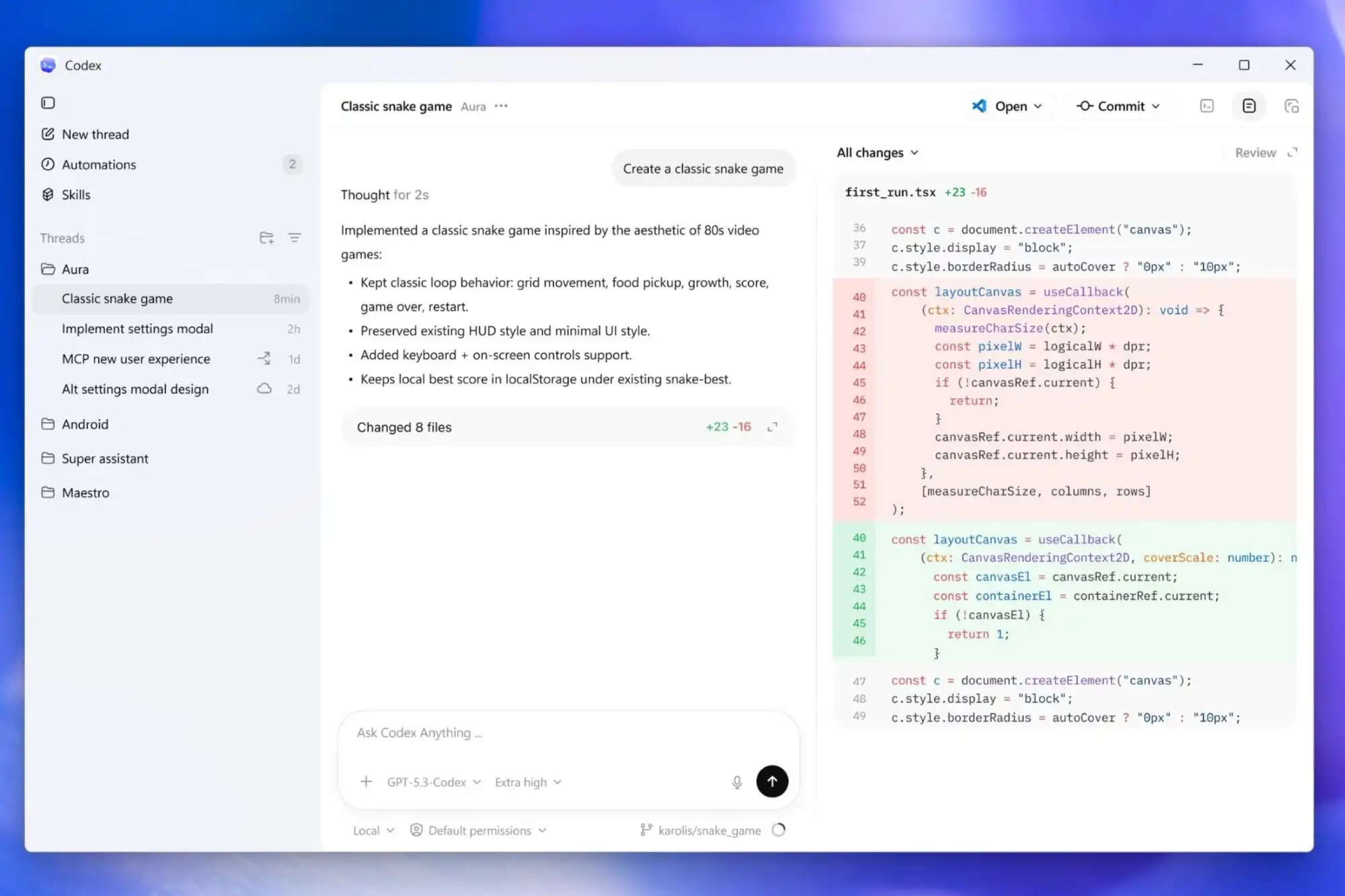
OpenAI has released a native Windows desktop version of its Codex app, an AI-driven coding assistant that leverages...

The new Ryzen AI 400 series delivers Zen 5 performance but trades PCIe lanes for efficiency, leaving high-end GPU u...

A new variant of the entry-level RTX 5050 with 9 GB GDDR7 memory could improve efficiency, but supply constraints a...

A retrospective look at the technical and creative hurdles that shaped Deus Ex: Invisible War, revealing how engine...

A classic competitive shooter, long thought buried under its successor, has resurfaced on Steam—without fanfare or...

Google and Epic Games have resolved their dispute, allowing Fortnite to return to the Google Play Store while intro...

A rare in-game painting, priced at the game’s maximum gold cap, became the target of a collective puzzle hunt. One...

Lamptron has introduced silver variants of its HC060 and HM049 hardware monitors, designed for real-time system mon...