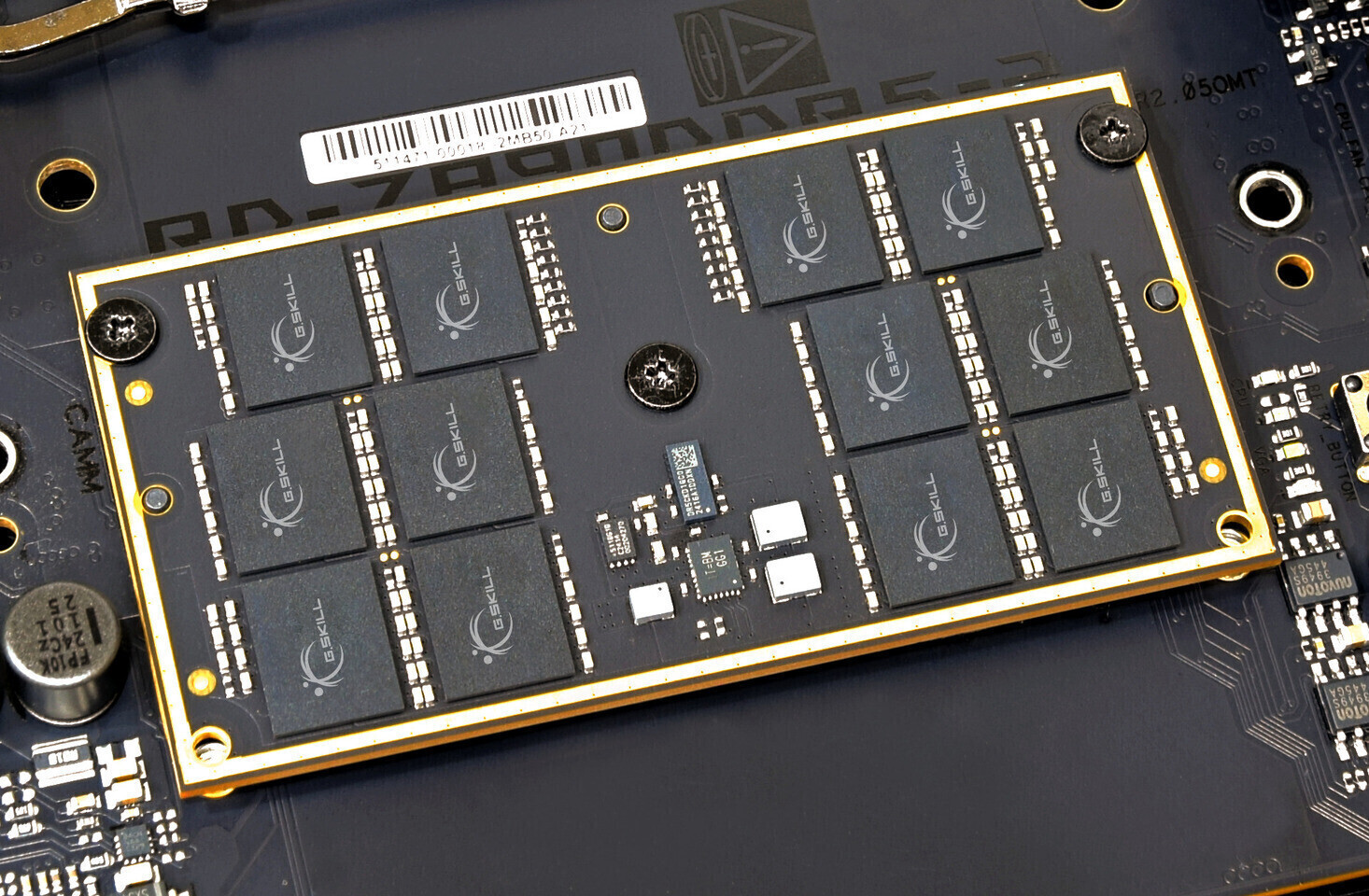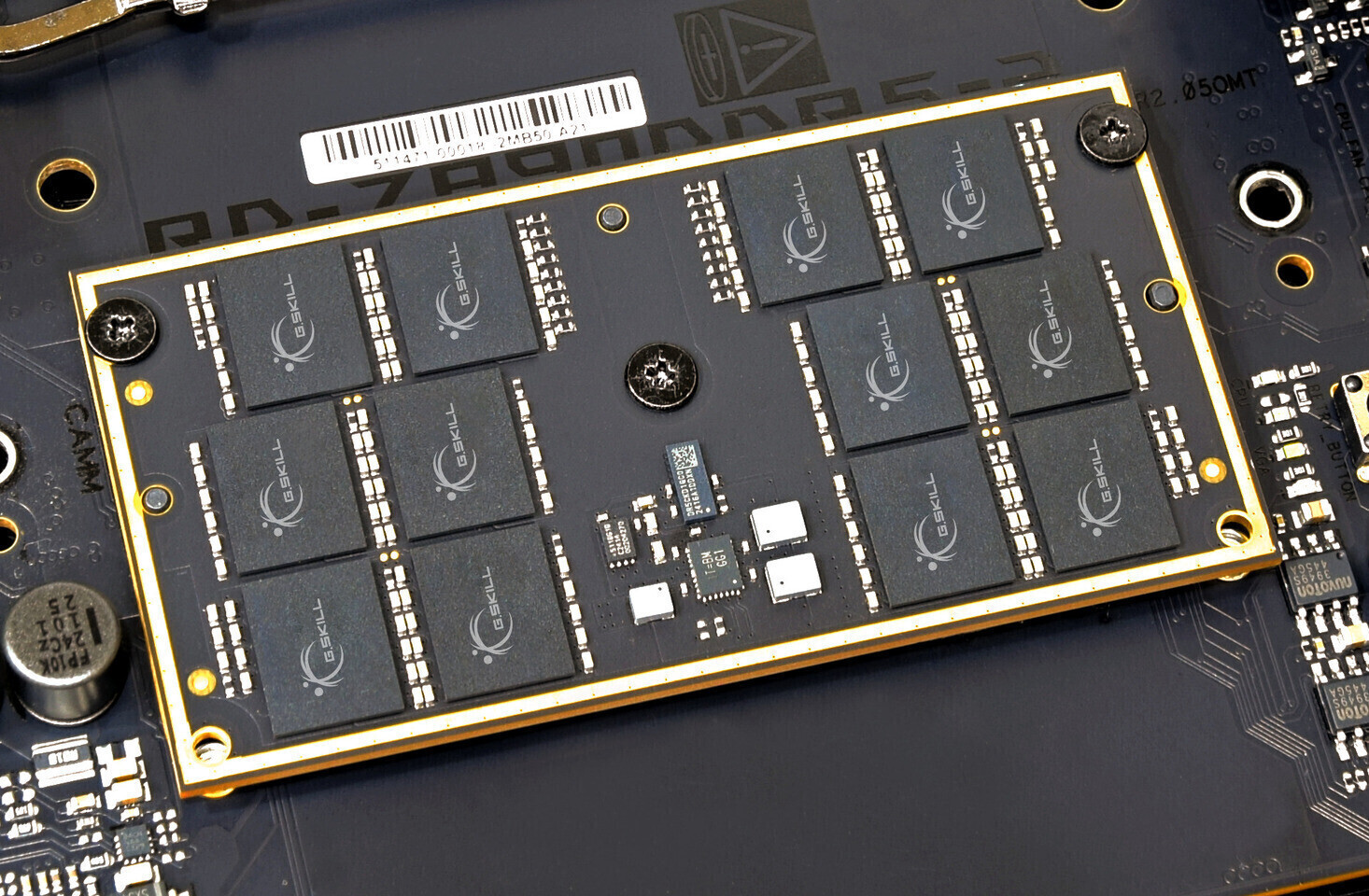
The DDR6 standard is poised to redefine performance benchmarks with speeds up to 17,600 MT/s, but its adoption hinges on overcoming significant engineering challenges. This article explores the tradeoffs behind...








The Boneyard’s Dybbuk isn’t just a rolling, dodging nightmare with 85 hit points—it punishes the player who defeats...

A new game from Strange Scaffold turns infant futures into a high-stakes gamble—where even the most calculated bets...

The upcoming *Age of Wonders 4: Rise from Ruin* expansion introduces the harefolk—nomadic, rabbit-like survivors of...

Early analysis suggests the Nintendo Switch 2’s version of *Final Fantasy VII Rebirth* may deliver smoother perform...

Owners of select AMD CPUs, GPUs, or laptops can now claim a free copy of Crimson Desert—a highly anticipated open-w...
China’s largest memory manufacturer is reallocating a significant portion of its DRAM production to high-bandwidth...

Optoma has launched the UHZ36, a true 4K UHD laser projector designed to deliver cinema-quality visuals with minima...

Walmart’s entire lineup of Onn-branded 4K Google TV streaming devices—including the $29.88 Onn 4K Plus—are sold out...

The origins of Fallout 3’s iconic slow-motion combat system trace back to an unexpected source: a racing game’s des...

With Discord enforcing mandatory ID checks for adult access, users are left wondering: *What now?* The answer might...