A new high availability architecture combines Scality's storage expertise with Veeam's backup solutions, promising enterprise-grade resilience without the complexity. IT teams must weigh performance claims agai...




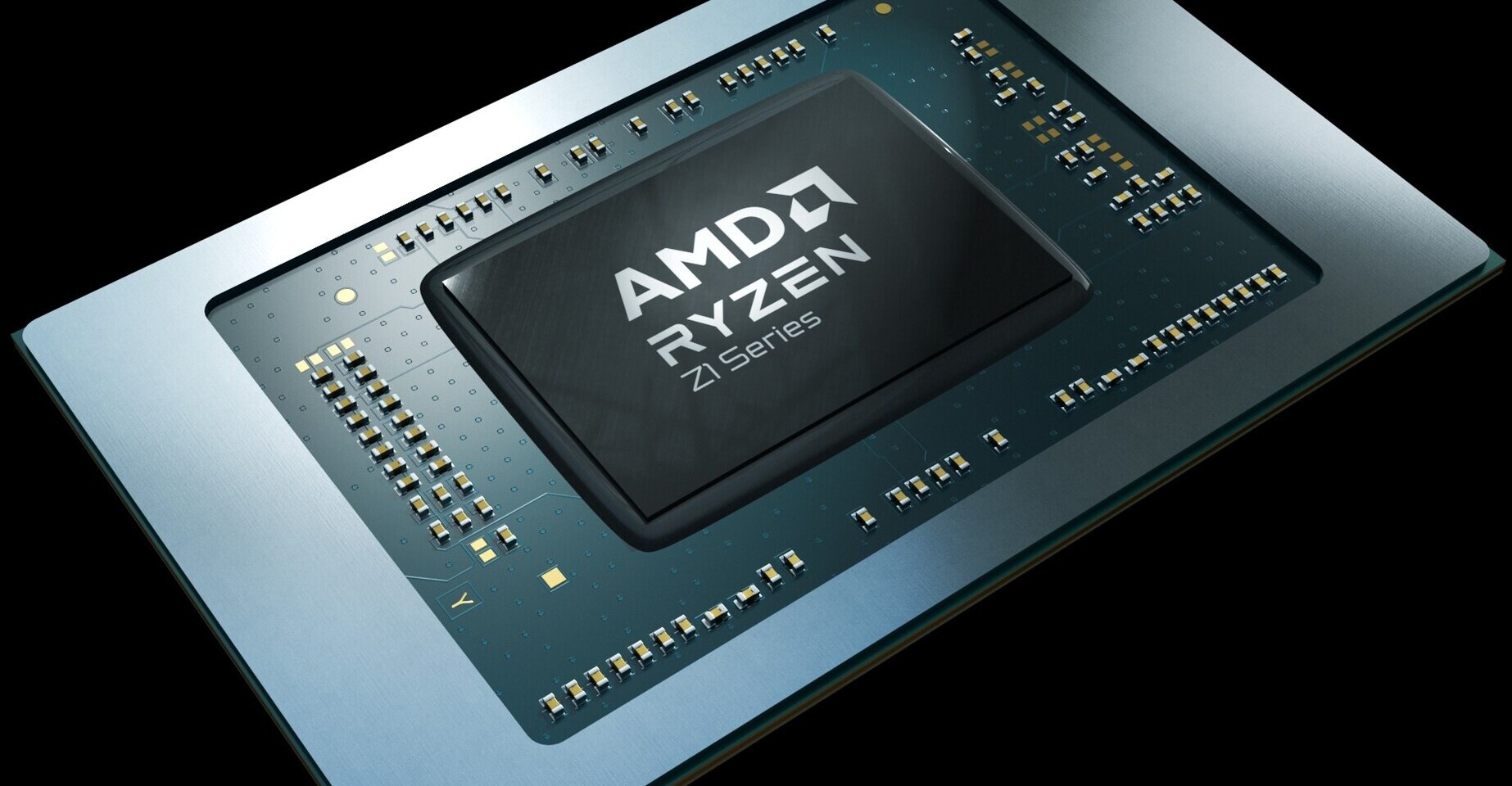
The ASUS ROG Ally handheld, powered by AMD’s Ryzen Z1 Extreme SoC, has received its first driver update in six mont...
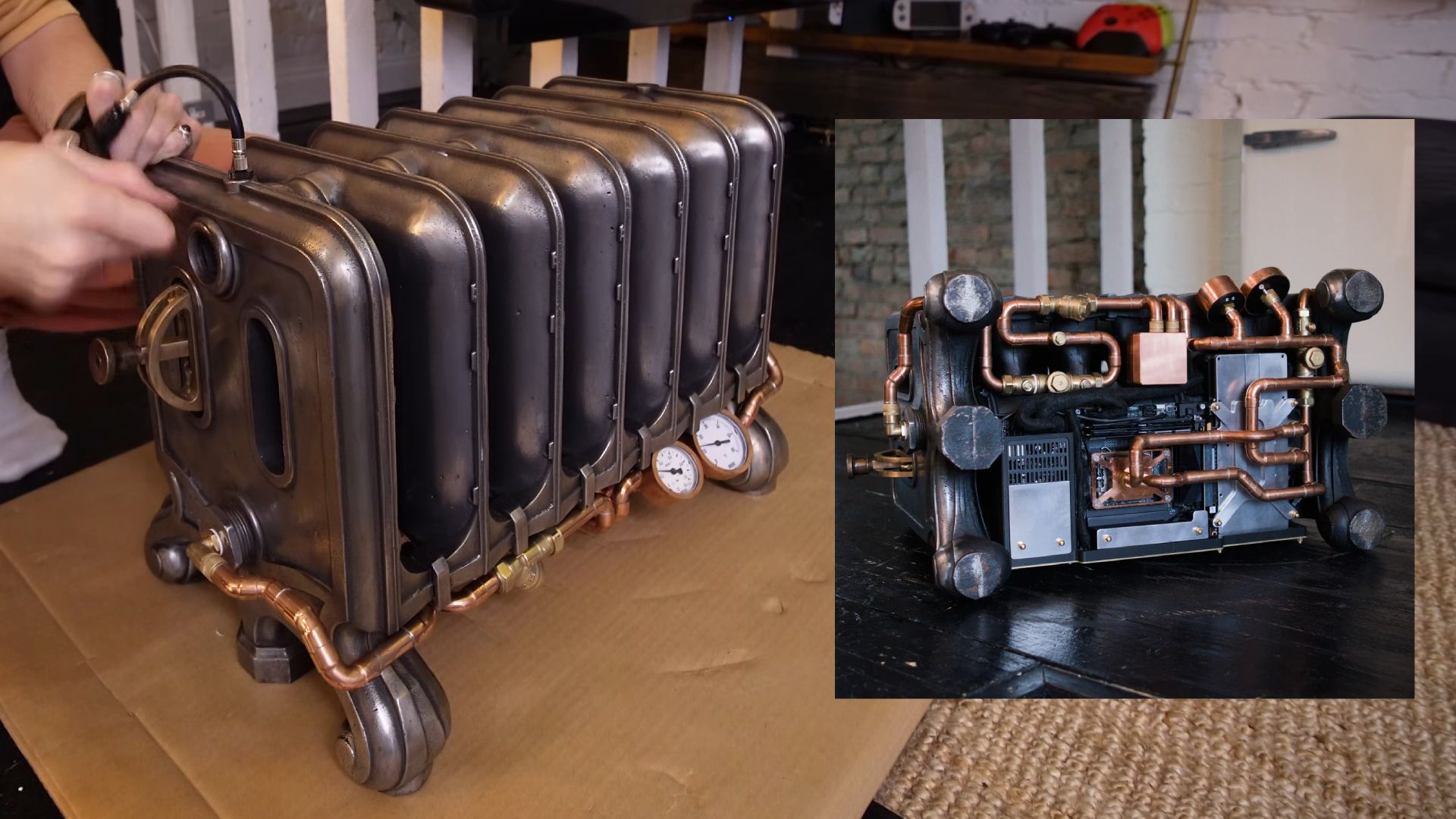
A custom PC build repurposed a cast-iron radiator as its primary heat exchanger, resulting in a monstrous yet funct...

A mini PC with 32GB RAM, triple 4K display support, and a Ryzen 5 7430U now sits at a record low of $340—posing a d...

Blizzard’s latest experiment in *Overwatch* isn’t just another hero shooter—it’s a 6v6 catfight where keyboard spam...
The first public demo of Distant Shore: BRETAGNE—a high-octane blend of parkour and magnetic physics—lands on Steam...

The $8/month YouTube Premium Lite plan now includes background playback and offline downloads, narrowing the gap wi...

The new integration between Malwarebytes and ChatGPT marks a turning point in how users detect scams, blending AI-d...

Capcom’s latest attempt to reconcile *Resident Evil*’s survival roots with its modern action identity exposes a fun...
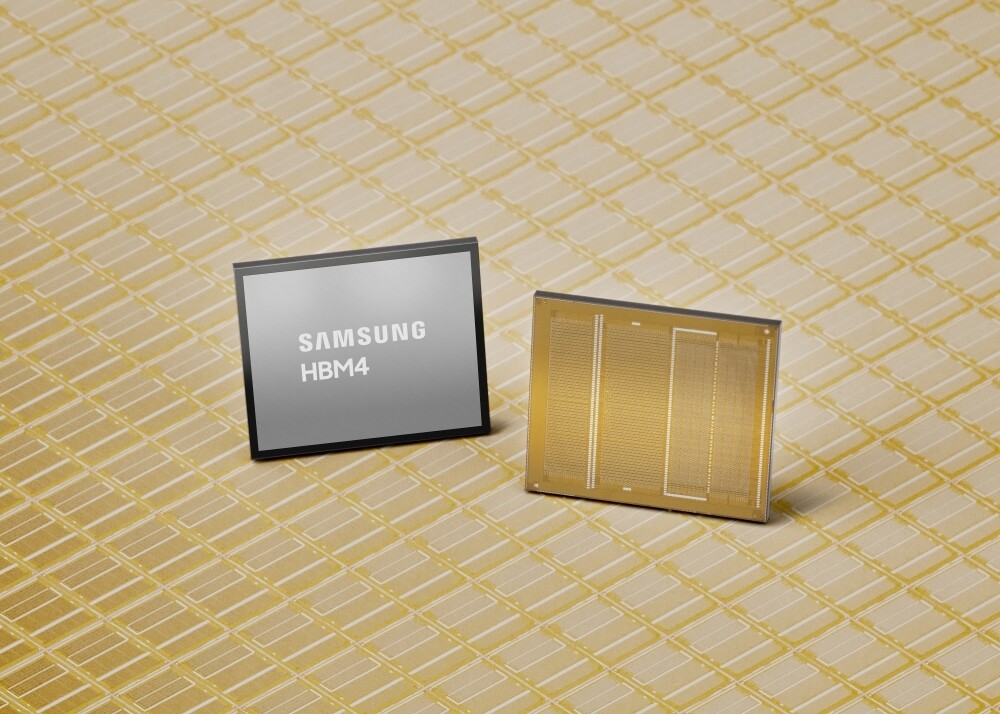
Samsung is ending 2D NAND production to reallocate its aging Hwaseong facility for high-bandwidth memory, aiming to...

The UltraGear EVO 52G930B brings a massive 5120x2160 resolution, 240Hz refresh rates, and DisplayHDR 600—but with a...