The DDR6 standard is poised to redefine performance benchmarks with speeds up to 17,600 MT/s, but its adoption hinges on overcoming significant engineering challenges. This article explores the tradeoffs behind...



A new $19.99 multi-site WordPress hosting plan from Hostinger allows users to host up to 50 sites with shared resou...

A refurbished version of the Microsoft Surface Pro 6 is now available for just $229, offering a compelling entry po...

Real-world testing of OPPO’s Find N6 shows significant screen damage after minimal use, casting doubt on Apple’s ma...

A food seasoning giant’s AI chip strategy could reshape the market, but real-world performance and long-term roadma...

The ASUS Zenbook A16, powered by the Snapdragon X2 Elite Extreme, demonstrates superior sustained performance under...

The RPCS3 emulator has integrated encrypted PlayStation 3 disc image support, a major leap that could redefine how...

A groundbreaking collaboration between Qualcomm and CXMT aims to redefine smartphone memory, promising faster speed...

A batch of Xbox controllers arrived without batteries, forcing Microsoft to launch a replacement program. The issue...
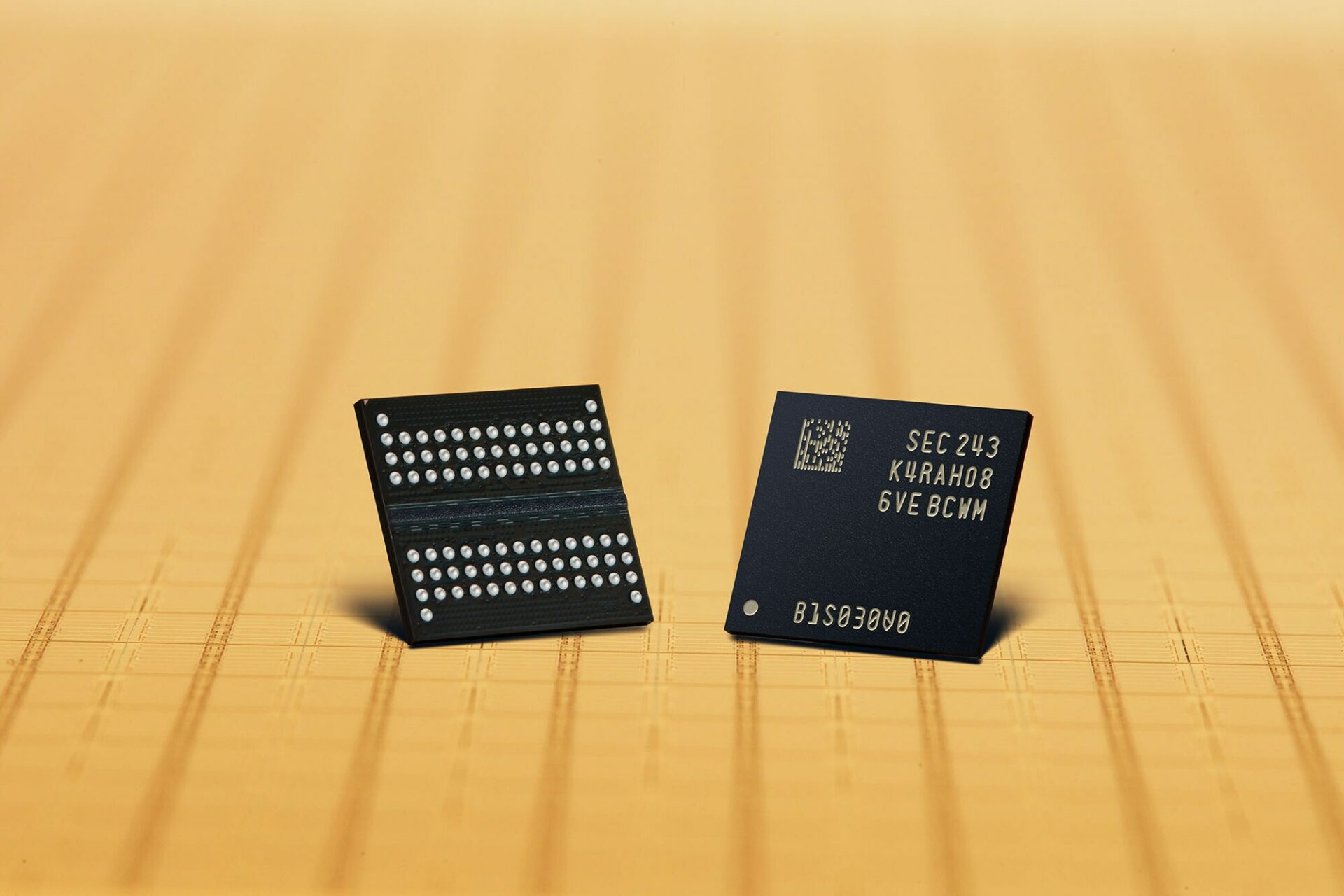
A previously overlooked segment—memory chips—has overtaken major tech companies in profitability, signaling a funda...

The Crimson Desert GPU now supports Intel's Arc graphics, including XeSS 3.0 frame generation, marking a shift towa...