A newly discovered Linux vulnerability allows attackers to bypass security checks and gain elevated system access, posing a serious risk to servers and workstations. Experts warn of active exploitation attempts...






A breakthrough GPU architecture delivers sustained high performance while significantly reducing power consumption...
A new ruggedized access point combines Wi-Fi 7 performance with industrial-grade durability, designed to handle ext...

The Lenovo IdeaPad Slim 3X stands out as a rare Windows alternative to the MacBook Neo, offering double the RAM and...

Apple's push for a foldable iPhone faces growing material supply chain hurdles that could extend its timeline beyon...

A new mod for Crimson Desert introduces dynamic grass shadows and optimized LOD settings, enhancing visual quality...
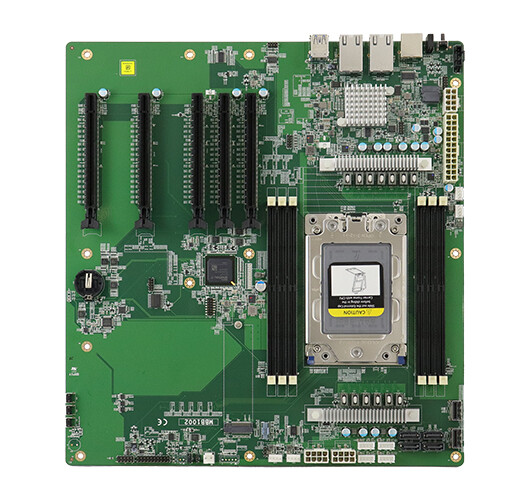
The IBASE MBB1002 stands out as a purpose-built platform for edge AI, combining AMD EPYC Embedded 8004 support with...

Two new docking stations leverage Thunderbolt 5 to deliver advanced connectivity, high-capacity storage, and robust...

Eight refined efficiency measures in Windows 11 that collectively streamline daily operations for small businesses,...

A new mechanic in Crimson Desert allows players to secure full-health revives without permanent costs, reshaping te...

A new gaming monitor with OLED technology and a 144Hz refresh rate challenges the status quo in mid-range displays,...