The new RTX 50 series GPUs promise significant efficiency gains, but their higher thermal output may challenge small businesses to rethink cooling strategies without compromising performance.




AMD’s RDNA 5 architecture, slated for a 2027 release, is poised to challenge performance benchmarks with a focus on...

A high-profile chip industry executive joins Intel’s foundry business, signaling a renewed focus on competing in th...

Lexar's new ARMOR 700 Portable SSD and SILVER PLUS microSDXC card target professionals with massive storage needs,...

Valve's latest Proton update introduces Wine 11 performance gains, including NTSync kernel driver support, while al...

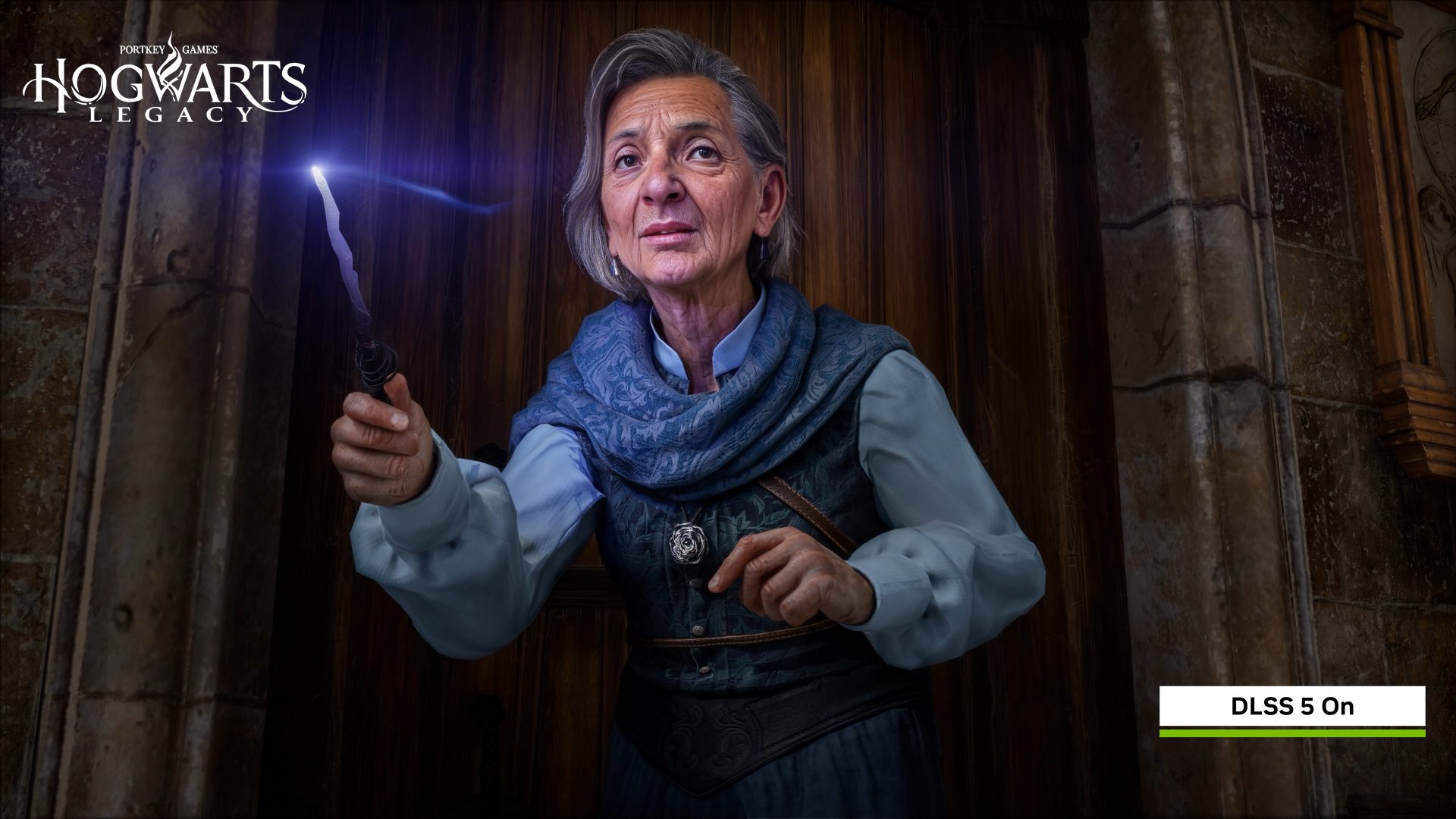
Capcom’s sci-fi action adventure PRAGMATA is now available via NVIDIA GeForce NOW, offering cloud gaming without ha...

A new repair process for the iPhone 17 Pro Max aims to restore units with cosmetic damage to near-pristine levels,...

A four-day free giveaway of 'Graveyard Keeper' on Steam generated $250,000 in revenue and spiked player counts to 4...
The Corsair Vengeance RGB DDR5 6400MHz 32GB kit delivers high-speed memory performance at a competitive price point...
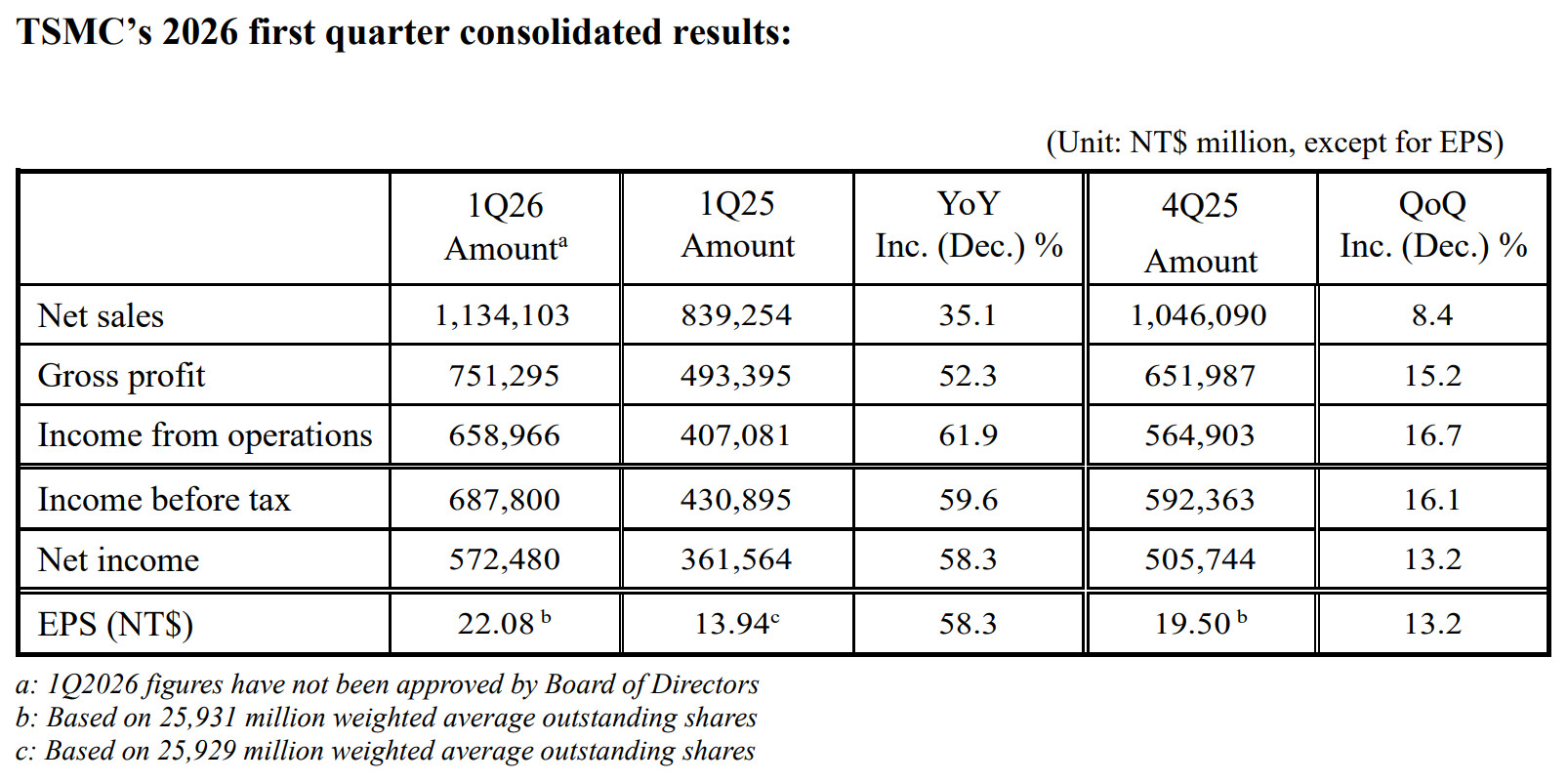
TSMC's latest financial results highlight a strategic shift toward advanced packaging, signaling deeper changes in...

A new entry in the Metro series promises to return players to the claustrophobic tunnels of post-nuclear Moscow, wi...